Oracle has privately acknowledged to select customers that it suffered a security breach impacting its legacy Oracle Cloud infrastructure (Gen 1, aka Oracle Cloud Classic). While Oracle publicly maintains that “Oracle Cloud was not breached,” leaked data, threat actor claims, and third-party verifications indicate that a significant compromise occurred involving sensitive identity data.
🔍 What Actually Happened?
- A threat actor gained access to Oracle Cloud Classic (Gen 1) systems as early as January 2025, exploiting a Java vulnerability from 2020 to deploy a web shell and malware.
- The breach, discovered in late February, led to exfiltration of data from Oracle Identity Manager (IDM), including:
- Email addresses
- Hashed passwords
- Usernames
- CybelAngel, a cybersecurity firm, confirmed that Oracle informed select customers of the breach.
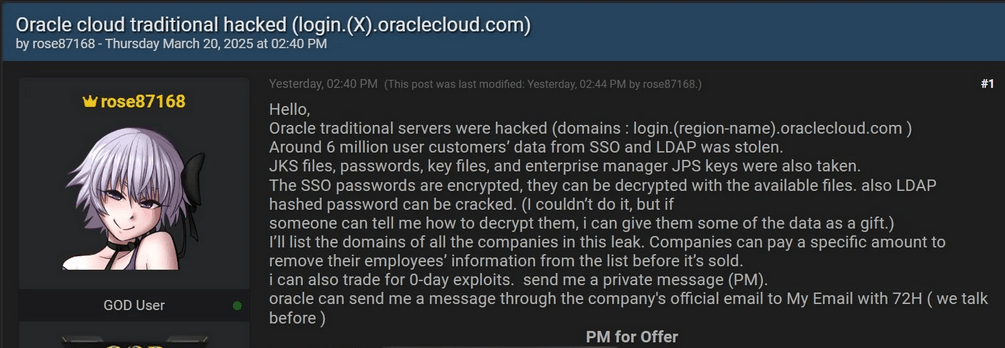
- A hacker using the alias “rose87168” listed 6 million data records for sale on BreachForums, and released:
- Sample LDAP data
- Database snippets
- Company lists tied to Oracle’s federated SSO login servers
- BleepingComputer independently verified samples with impacted organizations — confirming the leaked data is authentic.
Yet Oracle continues to publicly state:
“There has been no breach of Oracle Cloud. The published credentials are not for the Oracle Cloud.”
Cybersecurity experts argue that Oracle is playing with terminology, since Oracle Cloud Classic is still part of Oracle’s managed cloud stack, even if it’s technically a “legacy” service.
⚕️ Separate Oracle Health Breach Impacts US Hospitals
In addition to the Cloud Classic breach, Oracle has privately disclosed another incident involving Oracle Health (formerly Cerner) — its healthcare-focused SaaS platform.
Key Details:
- Breach discovered on February 20, 2025, affecting legacy data migration servers.
- Hackers used compromised customer credentials post-January 22 to access the systems.
- A threat actor named “Andrew” is extorting multiple US hospitals, demanding millions in cryptocurrency to prevent release of patient data.
- The actor has created clearnet websites to pressure victims into paying ransom.
Oracle Health has not issued any public statement, despite confirmation of the breach from affected healthcare providers and internal communications.
🧠 Critical Takeaways for the Cybersecurity Community
1. 🧱 Semantic Distancing Doesn’t Eliminate Risk
While Oracle claims “Oracle Cloud” wasn’t breached, the compromised infrastructure (Oracle Cloud Classic) was still actively managed and contained sensitive IAM data. Experts view this as semantic evasion rather than full transparency.
2. 🔐 Legacy Systems = Hidden Liabilities
The breach shows how outdated cloud systems, even if rarely used, can still hold critical access data and secrets — and may not be monitored as tightly as modern platforms.
3. 📣 Limited Transparency Undermines Trust
Both incidents reflect Oracle’s reactive, non-public approach to breach disclosure. Without timely and public transparency, customer trust — especially in healthcare — is at serious risk.
✅ What Should Organizations Do Now?
- Review Oracle integrations, especially federated SSO or legacy platform dependencies.
- Rotate credentials, especially if tied to Oracle Identity Manager or older services.
- Audit for LDAP usage, shadow access paths, and exposure via outdated identity systems.
- Monitor for leaked data matching your organization on dark web forums or breach intel platforms.
📌 Final Thoughts
While Oracle attempts to distinguish between its modern cloud offerings and its legacy infrastructure, the breach demonstrates that any part of the cloud stack — old or new — is a potential attack surface. Security teams must consider all components, especially those still handling identity and authentication, as critical assets.
Given the increasing volume of federated and third-party authentication models, even a breach in a “retired” system can lead to serious downstream risks.
Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.
